Image: Copilot AI
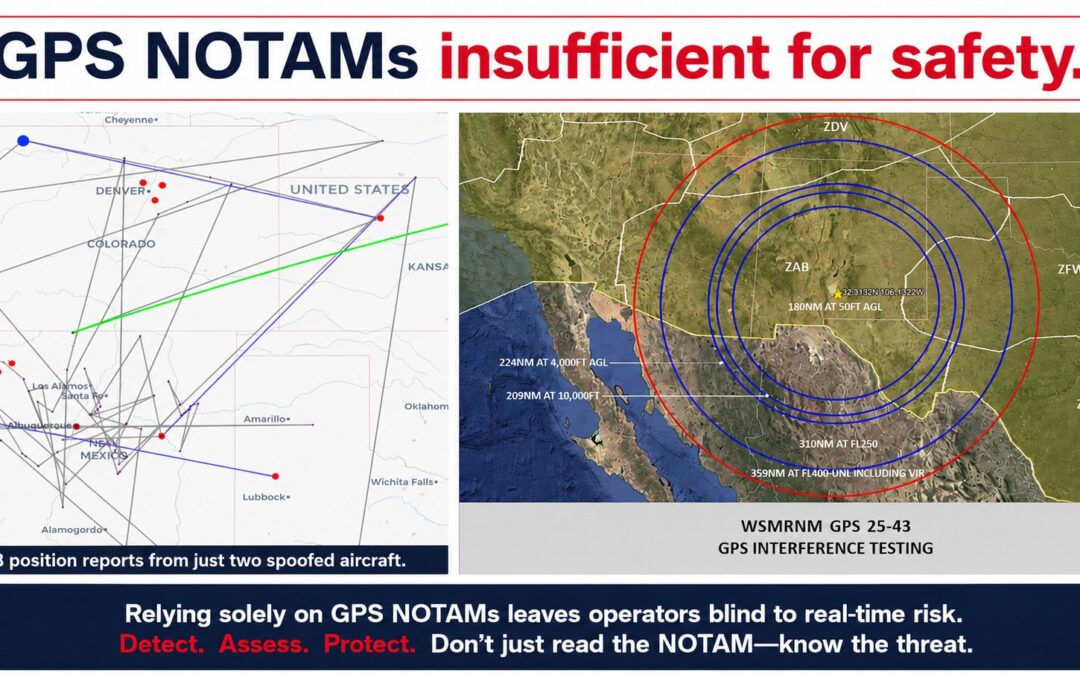
What’s new: Information that Iran used GPS spoofing to interfere with Starlink’s service in that country.
Why it’s important: It is another great example of how systems you might not expect depend upon GPS and the vulnerabilities that introduces.
What else to know: Iran has a long history of spoofing GPS as a part of domestic and international politics. Some examples:
- 2011 – Capturing a CIA drone operating in Afghanistan and landed it at Iranian air base.
- 2016 – (Probably) Luring US Navy boats into Iranian waters and capturing them
- 2019 – Seizing a British tanker
- 2019 – (Probably) Luring a US drone into its waters and shooting it down
- 2024 – During war with Israel

Iran Strikes Musk’s Starlink—First ‘Electronic Warfare’ Attack
By Zak Doffman, Contributor.
Zak Doffman writes about security, surveillance and privacy.
The dangerous game of “cat and mouse” continues. Just hours after reports that “the jamming and packet loss situation in Tehran has improved significantly,” we have reports that Iran has escalated its attacks on Starlink. This is now unprecedented.
Cyber investigator Nariman Gharib posted on X Wednesday P.M., claiming the “first documented technical evidence of state-level GPS spoofing against consumer satellite internet.” This attack hit its mark. “Starlink stayed online but was barely usable.”