Image: RNT Foundation
Blog Editor’s Note: The author is President of the RNT Foundation.

Ukraine attacks changed Russian GPS jamming
Two Russian airbases deep inside the country were attacked on December 5: the Engels-2 base in the Saratov region and Dyagilevo near Ryazan. The next day an oil tank at the Kursk airfield closer to the border with Ukraine was hit and set on fire.
Reports from Russian witnesses and unofficial sources in Ukraine indicate that the attacks were carried out with UAVs operated by the Ukrainian military.
The Russian government has long interfered with reception of GPS signals, especially near and within its own borders. The early December attacks seem to have motivated an increase in this activity.
More Interference
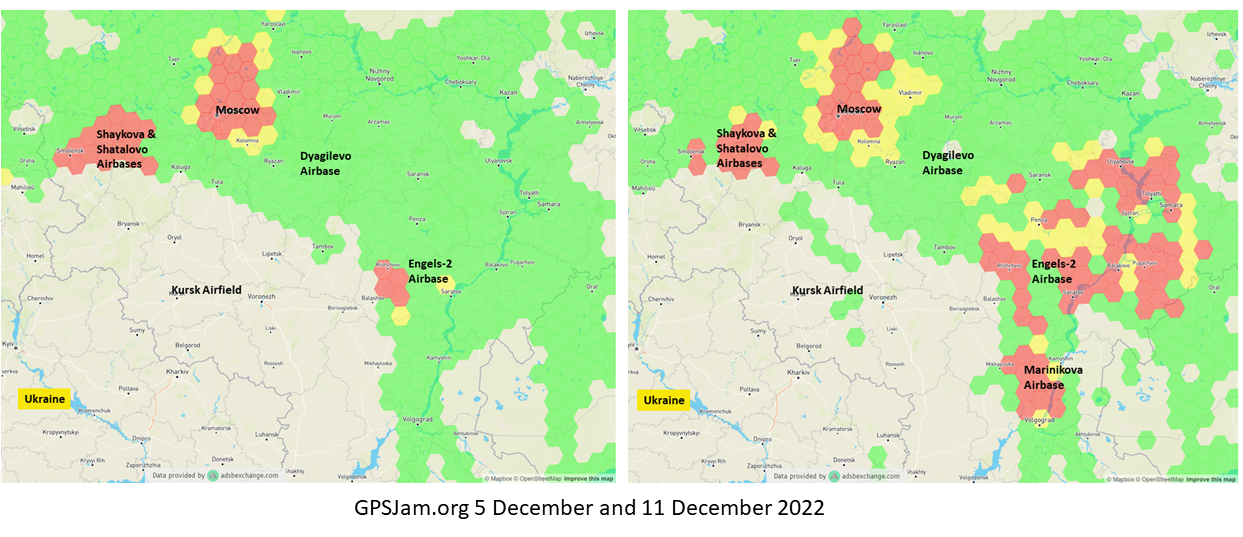
Information displayed by the website GPSJam.org indicates that, on the first day of the attacks, GPS interference was detected around Moscow, at two airbases to the east, and near the Engels-2 airbase.
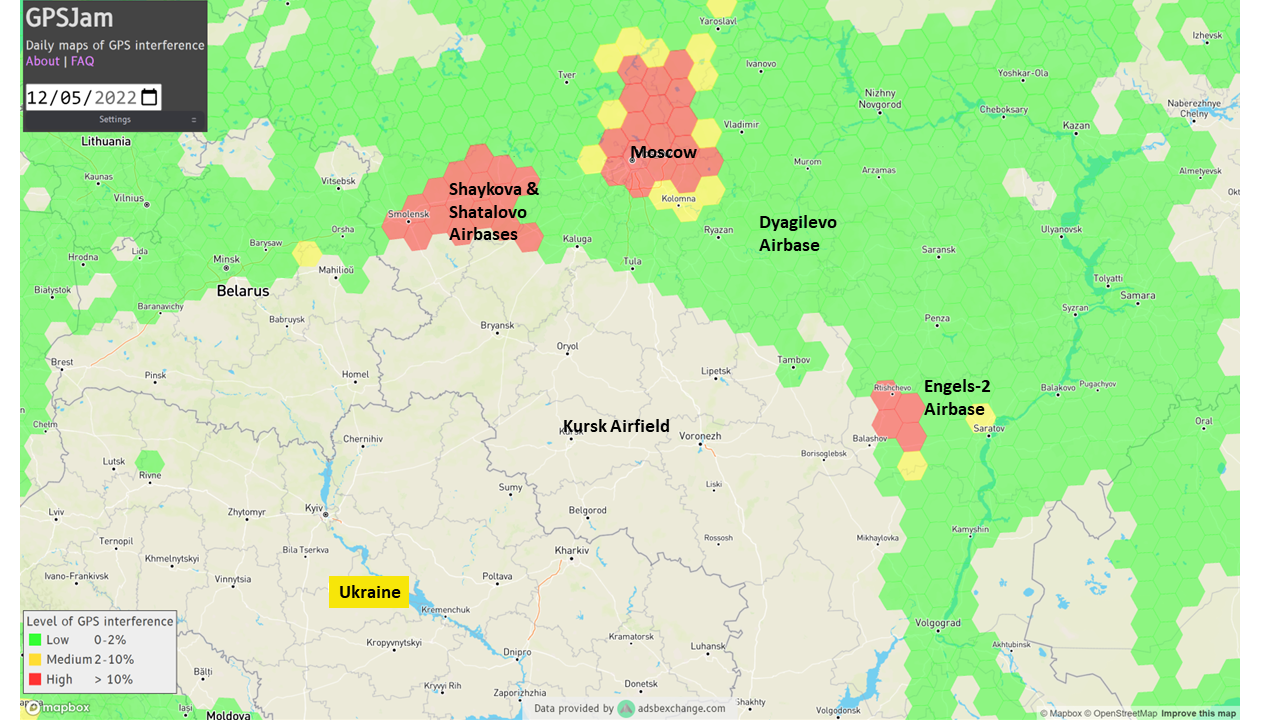
Image: RNT Foundation & GPSJam.org
GPSJam.org uses anomalies in crowdsourced aviation ADS-B data as an indicator of unreliable GPS signals. Note that no such information is available for much of Ukraine as commercial aircraft have been avoiding the airspace since the beginning of the current conflict.
The GPSJam.org depiction of the region six days after the attacks is quite different and has stayed much the same ever since. It seems to show greatly increased interference in the vicinity of the Engles-2 airbase, and new interference around the Marinikova airbase to the south along the Volga River.
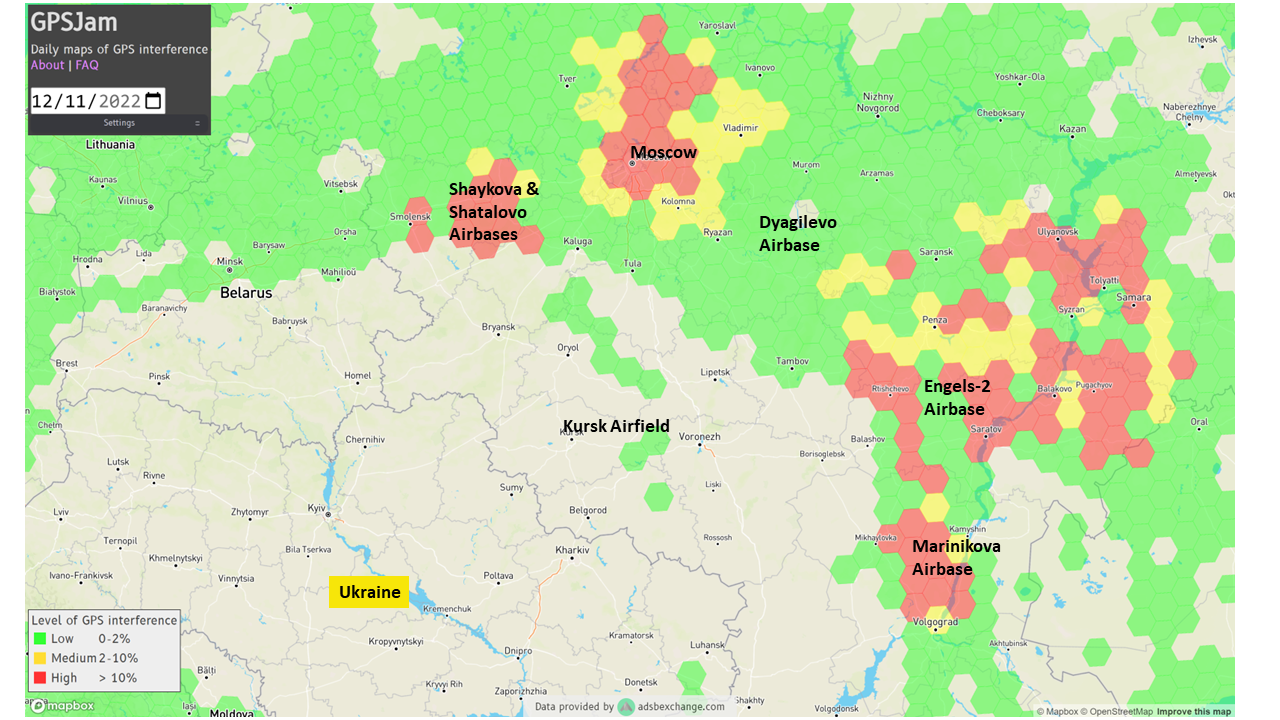
Image: RNT Foundation & GPSJam.org
A History of Jamming and Spoofing
The Russian government has been deliberately and systematically interfering with GPS signals in some places since at least 2016.
An article in the Moscow Times that year bragged “The Kremlin Eats GPS for Breakfast.”
The article documented a tech podcaster’s discovery that GPS L2 and L5 signals were being jammed and GPS L1 was being spoofed in the vicinity of the Kremlin. The combination of jamming and spoofing caused receivers in the area to report that, rather than being downtown, they were at the Vnukovo international airport some 20 kilometers away.
The author of the article speculated the spoofing was to protect government officials and buildings from surveillance and attack by UAVs. Since 2013 most larger UAVs have been programmed by manufacturers with the locations of airports and to avoid them. Making UAVs near the Kremlin believe they were at an airport could be an effective part of an overall defense system by causing them to avoid the area.
In 2017 the Resilient Navigation and Timing Foundation examined maritime AIS data and found similar spoofing activity had been occurring in the Black Sea for at least two years. A 2019 report by the nonprofit C4ADS expanded upon this work and revealed spoofing activity at various times and places across Russia. Almost 10,000 instances were documented across ten locations between 2016 and 2018. The report also linked much of the spoofing to the Russian Federal Protective Service and movements of senior government officials. This reinforced the idea that the spoofing was part of VIP protection efforts.
Questions Abound
It is easy to conclude that Russia’s recent increases in interference activity were in reaction to the UAV attacks on December 5 and 6.
Western intelligence and military officials may be arriving at additional conclusions and asking themselves some intriguing questions. One might be why it took six days after the first UAV attack to implement the new interference scheme. The report by C4ADS made it clear that Russian equipment used for wide area spoofing is quite portable.
Perhaps the delay was one of decision making. Some observers have commented that much of the direction for the current conflict comes directly from the top, rather than being delegated to field commanders. It could well be that it took that long for the Kremlin to realize that UAVs were involved and direct equipment to be deployed.
Another question likely being asked is about the selection of locations where interference is being used. Interference activity was observed at the Engels-2 airbase before it was attacked. This seems to have greatly increased after the attack. Airfields at Dyagilevo and Kursk were also attacked, but no interference activity has been observed at either location.
At the same time, substantial new interference activity has been observed at the Marinikova airbase, which was not attacked. There are likely several contributing factors to why some locations have been protected with jamming and/or spoofing and some not.
While Russian forces have a fearsome reputation for electronic warfare and their ability to interfere with GPS signals, the amount of equipment and the number of trained operators may be limited. C4ADS’ finding that spoofing equipment was moved around with VIPs rather than permanently located around the nation could indicate a limited amount.
This would mean that the bases and facilities to be protected must be prioritized. The lack of interference around Kursk and Dyagilevo could mean Russia sees them as less important, or less likely to be attacked again. New interference at Marinikova could mean it is a high value target and in need of protection.
Conversely, some of the new activity could be designed to deceive and draw Ukrainian fire away from higher value targets and toward lower ones. Such is the potential nature of military strategy in war.
Analysts are also probably asking questions about the effectiveness of jamming and spoofing as a defense against a determined UAV-operating opponent.
Interference had been detected at Engels-2 before it was successfully attacked by one or more UAVs. This likely shows that Ukrainian forces disabled any geofencing that might have been originally included as part of the UAVs’ original design. They may have also upgraded the UAVs’ navigation receivers with hardware or software to make them much more resistant to interference from the ground.
Navigation Warfare Increasingly Important
Regardless, the UAV attacks and observed changes in interference activity reaffirm the importance of navigation warfare in modern conflicts. Knowing the location of your forces and of your targets has always been important. In an era of precision strike and autonomous systems, robust and resilient navigation that resists or overcomes interference is even more important.
The U.S. military has long recognized this, establishing its Joint Navigation Warfare Center in 2004. The center focuses on the intersection of positioning, navigation, and timing with electronic warfare and cyber operations. Undoubtedly Russia has identical concerns and probably an equivalent organization.
The current conflict in Ukraine will continue to raise questions for both sides. Not in question, though, is the importance of navigation warfare to this conflict, and that it will be increasingly important in future ones.