Image: NASA
Blog Editor’s note: Interesting interview with Guy Buesnel from Spirent. Readers may find this bit from the article particularly interesting:
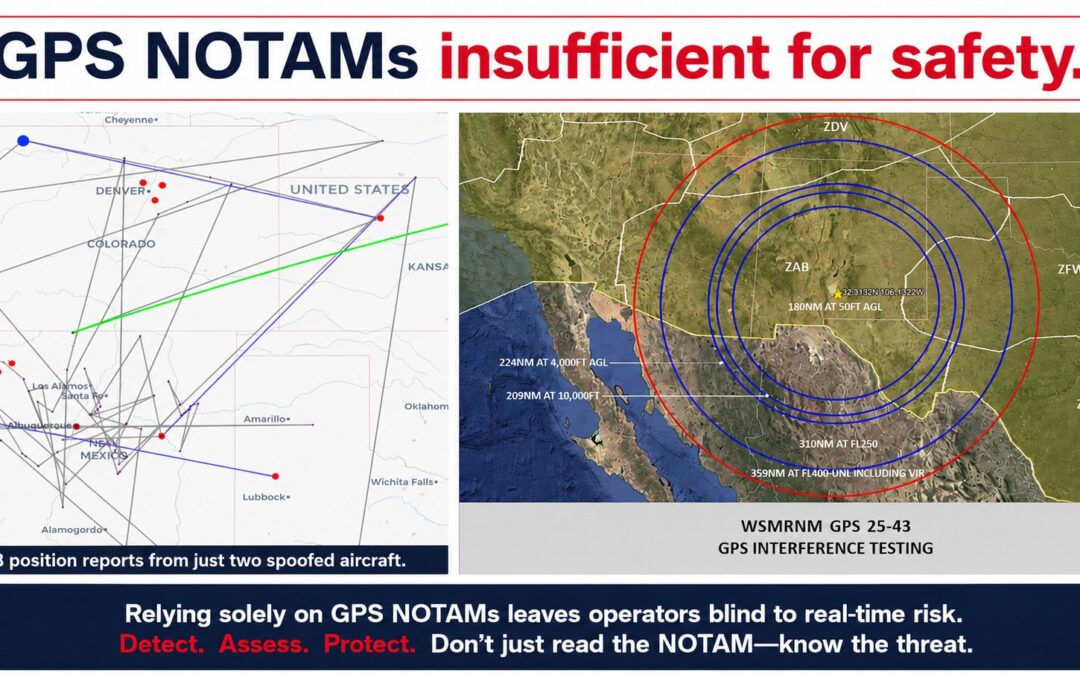
“With spoofing, even if a system is not a target, even if the attack does not fully succeed in taking over a receiver, we see that receivers exposed to a mixture of faked and authentic GNSS signals behave in unexpected and unpredictable ways.”
We hate it when we are going somewhere and our GNSS receiver beahves in ‘unexpected and unpredictable ways’ – don’t you? Especially if we are flying.
Full disclosure, Spirent is a corporate supporter of RNTF and Guy is a member of our International Advisory Committee.