Blog Editor’s Note: This article is a good overview of spoofing and its potential impacts.
The interviewer asks a very good question about incentives for spoofing GPS. While the article provides a general answer, it would be interesting to sit down someday with a group of our readers to see how many reasons for jamming and spoofing GPS/GNSS we could come up with. We could probably write a book.
Such an exercise would be key to developing policies and systems to disincentivize disruptions and protect GPS/GNSS signals and users.
Would be nice if there was someone in government interested in doing that. See our Op-Ed “No One is In Charge” this month in GPS World.
Full disclosure: Mr. Roi Mitt is interviewed for the article. He works for RNTF member Regulus.

Understanding GPS Data Spoofing
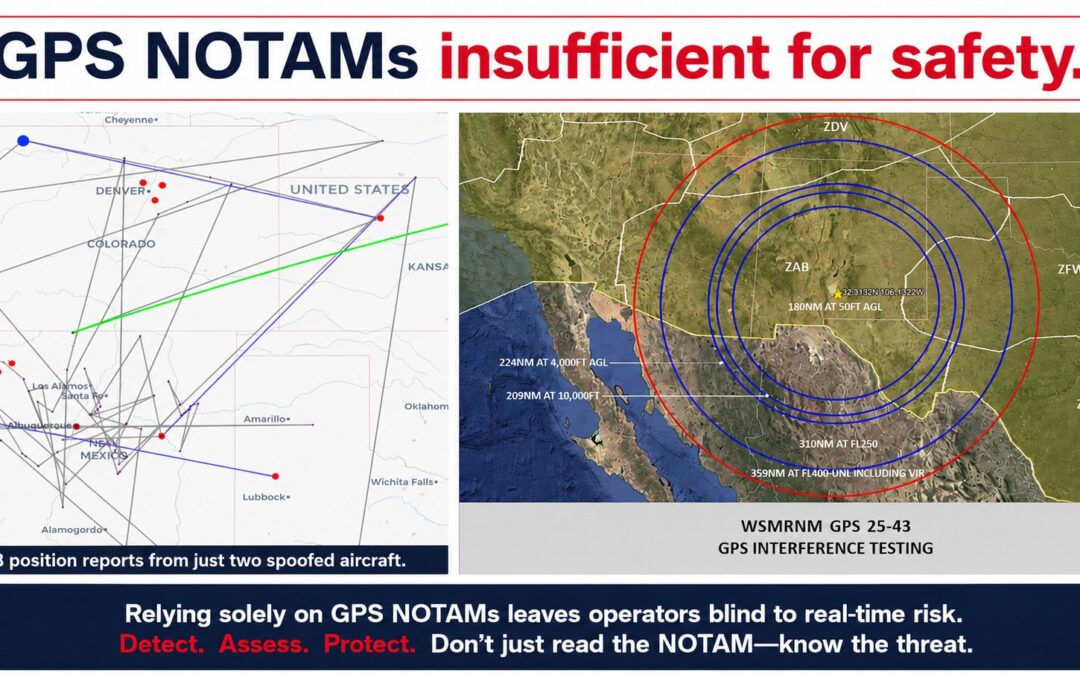
What’s behind GPS location spoofing and are there any recent example of these attacks?
The GPS system is an open signal without any encryption. This means any hacker can easily record and transmit this signal. This is true for all types of telecom technologies, including smartphones. GPS spoofing has occurred multiple times already. Some attacks are mobile-related, including spoofing used by UBER drivers to trick the app. A 2017 incident in a Miami conference affected all of the phones. Teenagers can even spoof their phones for Pokémon Go.
How does spoofing work and what are the incentives for it?
The spoofing signal is transmitting a fake satellite signal with more power than the one coming from space, essentially overpowering the real signal. This means that GPS location information can be controlled by a hacker. The typical device used to perform spoofing attacks is an SDR (software-defined radio).
As in any cyberattack, there are multiple incentives, both financial and criminal. Motives for hacking GPS include fun (cheating at Pokémon Go, a location-based game), an alibi (spoofing a mobile phone to change evidence), theft (spoofing a ride-sharing app to catch rides out of your reach), kidnap (spoofing a VIP\celebrity phone, so they can’t be tracked), and terror (spoofing multiple vehicles causing a mass accident).
What industries/applications depend on GPS locations?