Blog Editor’s Note: The below article from Ars Technica is sharply critical of the overt claims, and perhaps unstated but implied consequences, in Regulus’ recent briefings and press releases (full disclosure – Regulus is an RNTF corporate member). Note that while a Tesla was the primary subject of Regulus’ testing, the company found similar vulnerabilities in receivers used by other auto manufacturers.
What everyone seems to agree on is that the GPS/GNSS receivers and the vehicles are unnecessarily vulnerable. They don’t include software or hardware that could make them more resilient to interference. At issue, is just how vulnerable and what that means.
Selection of receivers in the US is entirely up to the manufacturer, as far as we know, since the US government has not specified any standards. In fact, last year RNT Foundation wrote to and met with the US Department of Transportation as it seemed to us that their planning for automated driving ignored these kinds of vulnerabilities.
While the US government has been less than proactive in this area, we have encouraged and are glad to see that SAE International has begun to act. In April they began a project to describe resilient PNT receivers. We hope that this recent publicity will encourage auto manufacturers to join the SAE effort.

Regulus has responded to critiques of their work by scheduling a webinar for July 11th to discuss their testing and do Q & A. This should be an interesting event for anyone interested in the topic. Register here.
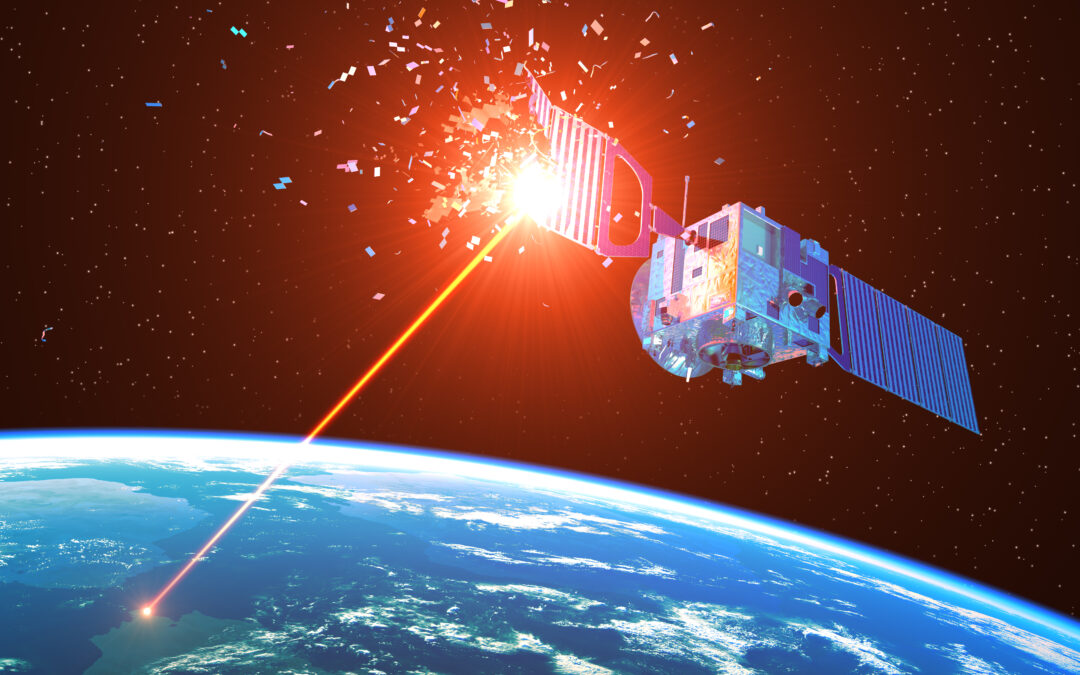
GPS HACKING WOES —
Claims of Tesla hack wide of the mark—we dig into GNSS hacking
This Tesla hack is plausible, but its implications were wildly overstated.
On Wednesday of this week, an Israeli firm called Regulus Cyber issued a press release stating that “spoofing attacks on the Tesla GNSS (GPS) receiver could easily be carried out wirelessly and remotely.” In the firm’s demonstration attack on a Model 3, “the car reacted as if the exit was just 500 feet away—abruptly slowing down, activating the right turn signal, and making a sharp turn off the main road,” according to Regulus. “The driver immediately took manual control but couldn’t stop the car from leaving the road.”
Tesla’s official response could best be described as “brusque.”
“These marketing claims are simply a for-profit company’s attempt to use Tesla’s name to mislead the public into thinking there is a problem that would require the purchase of this company’s product. That is simply not the case. Safety is our top priority and we do not have any safety concerns related to these claims.”Tesla official spokesperson
So, a company most of us haven’t heard of tells us that it’s demonstrated disturbing vulnerabilities in Tesla. Tesla, in effect, says said company is just looking for a buck and there’s no problem, but it doesn’t really provide any details. Where does the truth lie? That question necessitates a look at the merits of this specific Regulus-vs-Tesla claim—and then a broader glance into the history, technology, and possibilities of GNSS spoofing itself.
A closer look at the Regulus demo
If you read the opening paragraph of this article and thought that evil hackers took remote control of a car and made it go violently off-road, no strings attached, don’t feel bad—you were almost certainly meant to. But the reality is much different. The first, most obvious objection is that Regulus physically affixed an antenna to the roof of the Model 3 and wired it into its systems before the demonstration. That isn’t really the smoking gun it appears to be; it would’ve been possible to get the same effect with no antenna or wires, it just would have been extremely irresponsible (and most likely illegal).