.
A recent General Accountability Office (GAO) report is highly critical of the cyber security, or lack thereof, in U.S. weapons systems. One of the examples of cyber-attacks it lists is GPS spoofing.
The report, published this month, goes on to say:
“…weapon systems are dependent on external systems, such as positioning and navigation systems and command and control systems in order to carry out their missions—and their missions can be compromised by attacks on those other systems. A successful attack on one of the systems the weapon depends on can potentially limit the weapon’s effectiveness, prevent it from achieving its mission, or even cause physical damage and loss of life.”
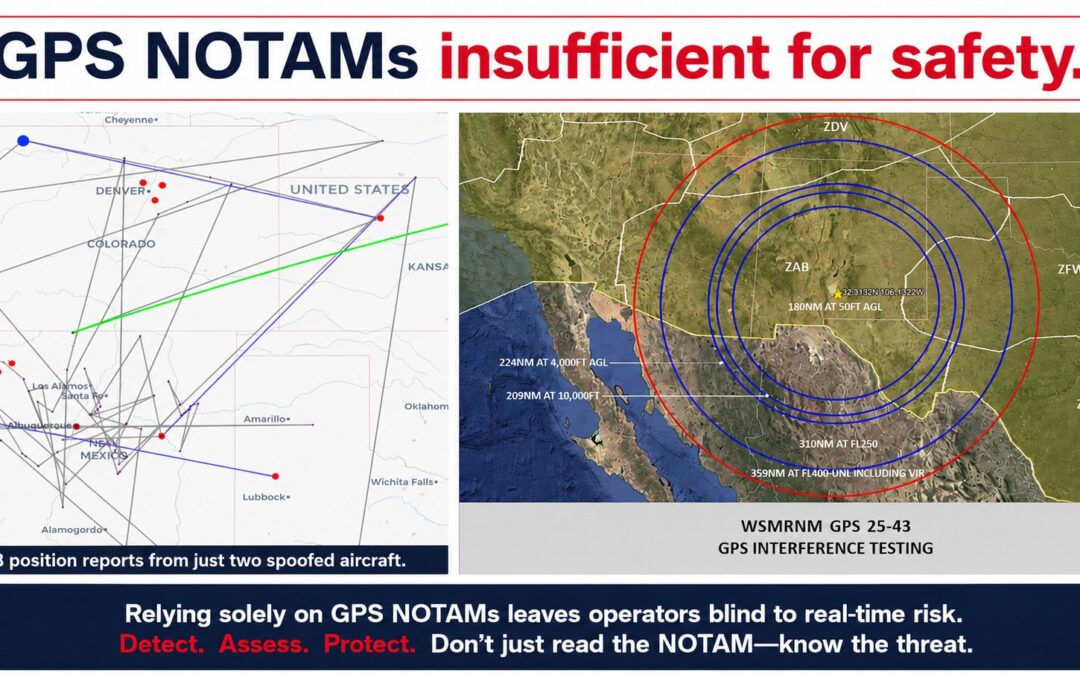
One method of spoofing that could be used is meaconing, or the interception and rebroadcast of navigation signals. This technique was first used by the British in WWII to divert German bombers away from factories and population centers. Meaconing can often defeat embedded security protocols, like the U.S. military’s M-code GPS, as it copies the entire signal, security protocol and all, so it is very difficult for the aircraft, ship, or weapons system to ignore.
The GAO study conceded that the Department of Defense was only “just beginning to grapple with the scale of vulnerabilities” to weapons systems.
Citing Russia’s reported spoofing of ships in the Black Sea, Britain’s Royal United Service Institute (RUSI) expanded upon GAO’s concerns and postulated that weapons could be redirected to targets other than those intended, such as hospitals. RUSI, an independent think tank engaged in cutting edge defense and security research, published a report on its website last week titled “Hackers can send British weapons to wrong target.”
In this report, written by Dr. Jack Watling, RUSI states, “The worst-case scenario is that you start launching precision strikes at, say, an enemy strongpoint and it lands on a hospital rather than on the target.”
In July 2017, Inside GNSS published Reports of Mass GPS Spoofing Attack in the Black Sea Strengthen Calls for PNT Backup.
Dana Goward is president of the Resilient Navigation & Timing Foundation
and a regular contributor to Inside GNSS.