Things seem to come in batches. Two reports by DHS of interest to our readers popped up on the radar the other day.
The first is one on mobile device security. Congress required the report as a part of 2015 appropriations and it was just submitted last month (April). Of specific interest are:
- A general lack of discussion of GPS jamming and spoofing impacts on mobile devices and their users,
- The failure to mention that cellular networks depend upon the GPS time signal, and
- A recommendation that a security best practice is to:
- “Restrict user and application access to hardware such as the digital camera, GPS, Bluetooth interface, USB interface, and removable storage.”
The second report is labeled “For Official Use Only (FOUO)” but has nevertheless somehow found its way to the internet. Titled “U.S. CRITICAL INFRASTRUCTURE 2025: A STRATEGIC RISK ASSESSMENT,” it includes this non-FOUO language (emphasis added):
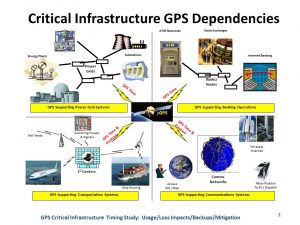
“(U) Global Positioning System: Cyber-physical systems also include GPS-based technologies, which have almost replaced paper maps in recent years. U.S. critical infrastructure sectors are increasingly at risk from a growing dependency on GPS for positioning, navigation, and timing. Awareness that GPS-supported services and applications are integrated in sector operations is somewhat limited, prompting the idea that GPS is a largely invisible utility. Therefore, dependence on GPS is likely to be significantly underestimated because many of the critical infrastructure sectors depend on the GPS timing function. OCIA assesses that the increasing convergence of critical infrastructure dependency on GPS services with the likelihood that threat actors will exploit their awareness of that dependency presents a growing risk to the United States.“
We would have thought that the folks who wrote the report on mobile device security would have included more about the GPS “silent utility” phenomenon. Also that last year’s assessment would have been widely published rather than being kept behind closed doors as a FOUO document.